A VPN tunnel is a private path through the public Internet. Tunneling is the process of encapsulating data within an IP packet.
 Checkout this video:
Checkout this video:
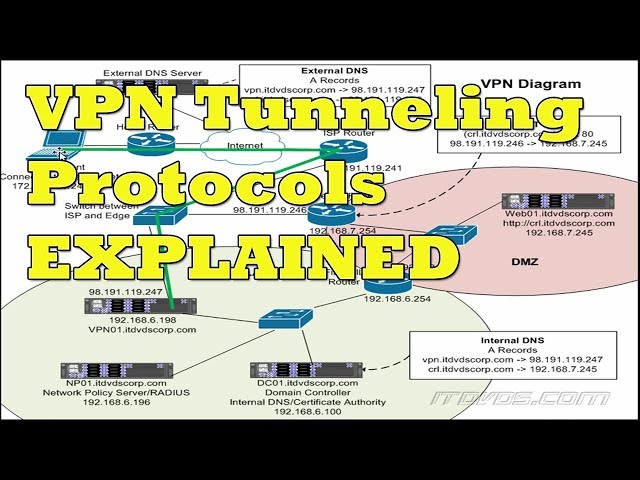
Introduction
In computer networking, tunneling is the process of sending data from one network to another. In a virtual private network (VPN), tunneling refers to the process of creating a secure, encrypted connection between two devices over a public network.
Tunneling works by encapsulating data in a secure protocol and sending it over the public network. The data is then decrypted at the other end and routed to the intended destination.
One of the benefits of using a VPN is that it can help ensure that your data is safe from eavesdroppers and hackers. Tunneling creates a secure, private connection between two devices, making it much more difficult for someone to intercept and steal your data.
Another benefit of tunneling is that it can help you bypass restrictions and censorship. If you’re trying to access a website or service that is blocked in your country, you can use a VPN to tunnel out of your country and access the content you’re looking for.
Tunneling can also be used to improve performance and speed. By routing traffic through a VPN server in a different location, you can often achieve faster speeds than if you were connecting directly to the website or service. This is because the traffic has less distance to travel and there may be fewer people trying to access the same server at the same time.
If you’re looking for a VPN service, make sure to choose one that offers strong encryption and security features, as well as fast speeds and good performance. Tunneling is an important part of how VPNs work, but it’s not the only factor to consider when choosing a VPN provider.
What is a VPN?
A VPN, or Virtual Private Network, is a tool that helps to keep your online activity private and secure. A VPN tunnels your internet traffic through an encrypted server, making it difficult for anyone to snoop on your activity or steal your data. A VPN can also help to get around firewalls and other restrictions that may be in place on your network.
How Does a VPN Work?
A VPN creates a secure, encrypted connection—which can be thought of as a tunnel—between your computer and a server operated by the VPN service. Anyone snooping on your activities on the local network will only see that you’re connecting to the IP address of a server belonging to your VPN provider. They won’t be able to see what you’re up to online. All of the data traveling between your computer and the VPN server is encrypted, ensuring that no one on the local network (including at your workplace or school) can see what you’re doing or where you’re going online.
What is Tunneling?
A VPN tunnel is a secure, encrypted connection between your device and another network. Tunneling is the process of sending data through this secure connection. When you tunnel data through a VPN, it prevents your ISP, government, or anyone else from spying on or monitoring your online activity.
Tunneling is a core component of how a VPN works. It encrypts your data so that only the VPN server can read it, ensuring that no one else can snoop on your online activity. It also allows you to bypass blocked websites and content filters.
Tunneling works by encapsulating data in an encrypted wrapper before sending it over the internet. When the data reaches the VPN server, it decrypts the wrapper and forwards the encapsulated data to its destination. This process happens in both directions, so all of your traffic is securely encrypted and private.
Types of Tunneling
Tunneling is a process of making an encrypted connection between two computers over the Internet. When you connect to a VPN, a secure tunnel is created between your device and the VPN server. This tunnel encrypts all the data that passes through it, making it impossible for anyone to sniff or intercept your traffic. There are different types of tunneling protocols that can be used in a VPN connection.
Point-to-Point Tunneling Protocol (PPTP)
Point-to-Point Tunneling Protocol (PPTP) is one of the oldest and most common types of VPN tunneling. It was developed in the mid-1990s by a consortium led by Microsoft, Ascend Communications, 3Com and others. PPTP uses a basic form of data encapsulation, in which each data packet is wrapped in a security header.
The most common form of data encapsulation for PPTP is the Generic Routing Encapsulation (GRE) protocol. GRE has been standardized by the Internet Engineering Task Force (IETF). In addition to GRE, PPTP can also use other data encapsulation protocols such as ATM or Point-to-Point Protocol (PPP).
Data encapsulation is used to secure the data being sent over the tunnel and to ensure that it is not modified in transit. When combined with IPsec encryption, PPTP provides a high level of security for VPN tunneling.
Despite its age, PPTP remains a popular choice for VPN tunnels because it is relatively easy to set up and does not require special software or hardware at either end of the tunnel. In addition, many routers and firewall devices support PPTP natively, which makes it easy to add to an existing network setup.
Layer 2 Tunneling Protocol (L2TP)
Layer 2 Tunneling Protocol (L2TP) is a VPN tunneling protocol that was developed by Cisco, Microsoft and Ascend Communications. L2TP is often used in conjunction with the Point-to-Point Tunneling Protocol (PPTP), which is also supported by Microsoft. A number of vendors have implemented L2TP/IPsec, including Cisco, Nortel Networks, Juniper Networks and Red Back Networks.
L2TP uses UDP port 1701 and can be tunneled over either IPsec or PPTP. L2PT/IPsec uses ESP or AH to provide confidentiality, authenticity and integrity. L2TP does not provide confidentiality on its own, but it can be combined with IPsec to provide encryption for the data that is being sent over the VPN connection.
L2TP has been deprecated in favor of L2TPv3, which is also known as L2TP over IP or simply L2TP/IP. L2TPv3 supports both IPv4 and IPv6.
Secure Sockets Layer (SSL)
Secure Sockets Layer (SSL) is a tunneling protocol that encrypts traffic between your computer and a VPN server. SSL is commonly used by online retailers and banks to protect the information of their customers. When you connect to a VPN server using SSL, your traffic is encrypted so that anyone who tries to intercept it will not be able to read it.
Internet Protocol Security (IPsec)
Internet Protocol Security (IPsec) is a set of protocols designed to secure Internet Protocol (IP) traffic. It is often used in Virtual Private Networks (VPNs) to protect traffic between two or more devices.
IPsec uses a combination of encryption and authentication to secure traffic. Encryption scrambles the data in a way that makes it unreadable by anyone who does not have the encryption key. Authentication verifies that the data has not been tampered with and comes from a trusted source.
There are two main modes of IPsec operation: transport mode and tunnel mode. Transport mode secures traffic between two devices, while tunnel mode secures traffic between two networks.
IPsec is often used in conjunction with another protocol called Layer 2 Tunneling Protocol (L2TP). L2TP provides a mechanism for transporting IPsec traffic over an unsecured network, such as the Internet.
Conclusion
In conclusion, VPN tunneling is a great way to keep your data safe and secure. By encrypting your data and sending it through a tunnel, you can be sure that no one will be able to see or intercept your data. Tunneling is also a great way to bypass firewalls and other restrictions that may be placed on your internet connection.
